At Asama AI, we’ve always believed that infrastructure shouldn’t just be fast and scalable,it must be inherently secure. As an AI Infrastructure Engineer, Asama doesn’t just monitor; it remediates. To do that effectively, we handle some of our customers’ most sensitive environments.
We are proud to announce that Asama AI is now SOC 2 compliant.
This wasn’t just a “check-the-box” exercise for us. It was a rigorous journey to validate the security foundations we’ve built since day one. Here is what got us here.
1. The Strategic Backdrop: Trust as Architecture
For many startups, compliance is seen as a hurdle, a mountain of paperwork to be tackled only when a deal is on the line. At Asama, we took a different path: Trust inbuilt as Architecture.
We believe that for an AI Infrastructure Engineer to be effective, trust must be a primary design constraint, not an afterthought. We designed our system for “auditability by default,” embedding the five Trust Services Criteria directly into our engineering DNA:
- Security: Protecting our systems against unauthorized access and potential vulnerabilities through continuous monitoring and automated safeguards.
- Availability: Ensuring our AI remediation platform is operational and accessible when your infrastructure needs it most.
- Processing Integrity: Guaranteeing that our AI agents perform their tasks accurately, timely, and according to authorised parameters.
- Confidentiality: Implement rigorous access controls and implement secret management to keep your sensitive organisational data protected.
- Privacy: Adhering to strict data handling practices to ensure personal and sensitive information is collected, used, and retained responsibly.
By treating these as architectural requirements rather than administrative layers, we ensure that trust is a living, breathing part of our technical stack.
2. Customers’ View: A CISO’s Perspective
When an organisation adopts Asama AI, there are dual evaluations at play. While infrastructure teams assess the functionality and Non-Functional Requirements (NFRs) of our platform, the CISO’s org looks deeper at security and compliance aspects of Asama.
For a CISO, evaluating an AI tool is an exercise in risk management. They are looking for a partner that won’t increase their attack surface or introduce vulnerabilities into their production environments. SOC 2 serves as the cornerstone of this evaluation, providing the evidence they need to verify our infrastructure is as resilient as our code. Here is what we believe it important for the CISO’s org:
- Demonstrates Tangible Security Commitment: SOC 2 provides objective proof of our dedication to Data Security Posture Management (DSPM), reassuring stakeholders that our practices are robust.
- Mitigates the Risk of Data Breaches: By focusing on the core principles of availability and integrity, we reduce the risk of unauthorized access or rogue autonomous actions.
- Boosts Trust and Competitive Advantage: It signals to security teams that we have already passed rigorous scrutiny, accelerating the enterprise partnership process.
- Ensures Compliance with Industry Standards: SOC 2 is vital for ensuring Asama AI integrates into highly regulated sectors, protecting everything from financial data to proprietary IP.
- Facilitates Better Security Governance: The audit process ensures our protocols are integrated into organizational policies and continuously improved, moving us from a “tool” to an “enterprise-grade solution.”
3. Timeline & Prep Work: Our 5-Week Sprint
While the mindset of trust was built in from the start, the formal execution was a concentrated 5-week sprint. We followed a rigorous 8-step preparation roadmap, leveraging automation to maintain velocity.
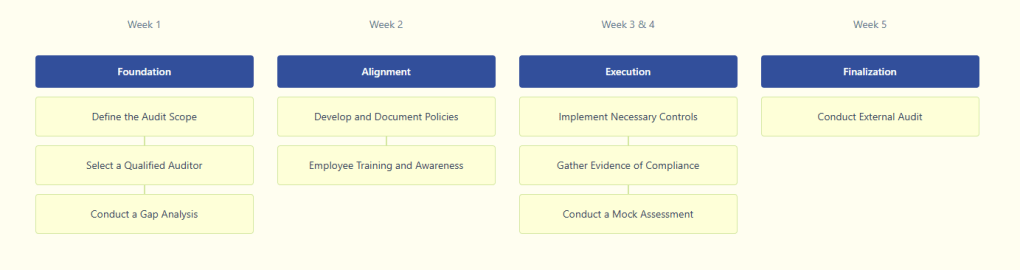
- Define the Audit Scope: We clearly identified which business units and systems were relevant to the audit.
- Select a Qualified Auditor: We partnered with an experienced firm that understands cloud-native AI infrastructure.
- Conduct a Gap Analysis: We identified where our current controls fell short of SOC 2 requirements.
- Develop and Document Policies: We formalised our internal processes into clear, actionable security policies.
- Implement Necessary Controls: We closed identified gaps by strengthening technical safeguards.
- Employee Training and Awareness: We ensured every team member understood their role in security.
- Gather Evidence of Compliance: We utilised automation to collect logs and configurations.
Conduct a Readiness Assessment: We ran a “mock audit” to ensure there were no surprises.
4. Key Learnings
The journey taught us that trust isn’t a badge you earn; it’s a system property you maintain. Here is what we learned from this journey:
- Automation is the Foundation: Manual evidence collection is the enemy of speed. Automated compliance allowed our engineers to stay focused on building while the system proved its own integrity.
- Culture Over Policy: A policy is just a document unless the team lives it. Every engineer at Asama understands that security is a core feature, not a side-hustle.
- Design for Trust Early: It is 10x harder to “bolt on” trust to a legacy system than it is to build it into a young, agile architecture.
5. Next Steps
While our sales team is ready to leverage this milestone to win more enterprise customers, our engineering team is already working proactively on our next set of milestones.
We recognise that if SOC 2 is implemented properly, 60+% of the architecture needed for GDPR and ISO 27001 is already in place. We are using this momentum to finalise:
- GDPR: Strengthening data privacy guarantees for our European partners.
- ISO 27001: Adopting the international gold standard for information security management.
- NIST AI RMF: Aligning our agentic AI workflows with the world’s leading AI management standards to ensure we remain the most responsible teammate in your stack.
Trust is earned in drops and lost in buckets. At Asama AI, we are committed to filling that bucket, one architectural decision at a time.
